Managed Detection and Response (MDR) service centers face a daunting challenge: sifting through a deluge of alerts and noise to identify genuine threats. Traditional approaches relying on static rules and log-based monitoring often generate excessive noise, leading to alert fatigue and missed sophisticated attacks.
To address this, MDR teams must adopt full contextual analysis. This means combining Cyber Threat Intelligence (CTI) with organization-specific data like asset criticality and user behavior. In this article, I will show you why contextual analysis is critical, the limitations of relying solely on CTI, and some practical solutions to enhance threat detection and response.
The Limitations of Static Rules and Log-Based Monitoring
Static rules are simple queries that rely on predefined patterns like known malicious IPs or attack signatures. They are effective for basic log/event analysis but fall short against complex attacks where connecting the dots is needed.
As a result, static rules generate excessive false positives, fail at prioritizing alerts properly, and burdens detection teams by forcing analysts to investigate each alert manually.
Let’s use a basic real-life scenario to illustrate this:
Issue: An MDR team receives multiple alerts for failed login attempts on a server, triggered by a static rule flagging excessive login failures. Without context, both a legitimate user mistyping their password and a hacker attempting a brute-force attack generate identical alerts, overwhelming analysts.
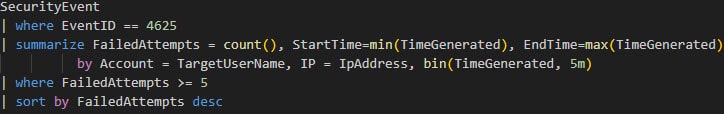
Example of a Microsoft Sentinel static rule relying exclusively on Windows logs to detect repeated failed user login attempts (5)
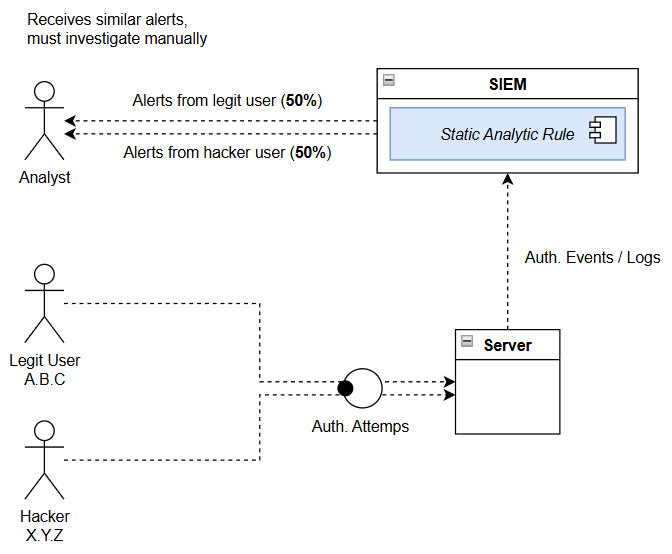
Possible Improvement: With contextual analysis, threat intelligence IOCs identify the hacker’s IP as part of a known botnet, triggering an immediate block. Meanwhile, the legitimate user’s IP, tied to an employee’s device, is given a higher threshold for failed attempts, reducing alert noise.
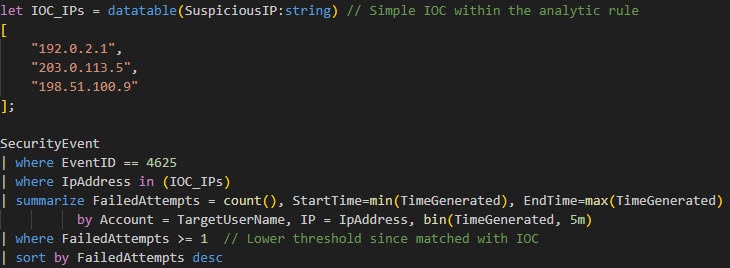
The same rule with an ultra basic IOC , with a lower threshold for suspicious IPs (1)
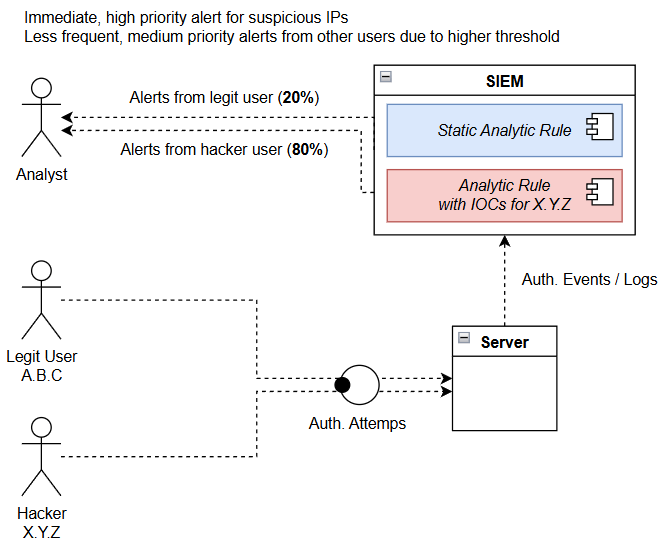
Conclusion: When properly implemented, contextual analysis using CTI helps prioritize real threats and reduce false positives. Rather than manually hardcoding IOCs directly into detection rules, MDR teams rely on CTI Platforms (TIPs) integrated with the SIEM to dynamically ingest and apply CTI feeds and indicators.
Threat Intelligence: A Partial Solution
We saw in the previous section that CTI, with its sets of IOCs like malicious IPs, domains, or malware signatures, is a powerful tool for spotting known threats. It’s like having a wanted list of cyber criminals and weapons at your fingertips to help your analysts quickly flag suspicious activity.
But here’s the catch: CTI only tells half the story. It specifically focuses on the attacker (who they are, what tools they use etc.) but it’s blind to your organization’s unique environment.
Let’s use another basic real-life scenario to illustrate this:
Issue: Imagine that malicious IP is targeting a low-value, public-facing website with static content. Should that trigger a red alert, pulling analysts away from more pressing issues? Probably not.
Worse, it might miss a subtle attack from a less-known IP targeting your critical assets (like a database stuffed with customer data), because generic threat feeds aren’t tailored to your specific infrastructure.
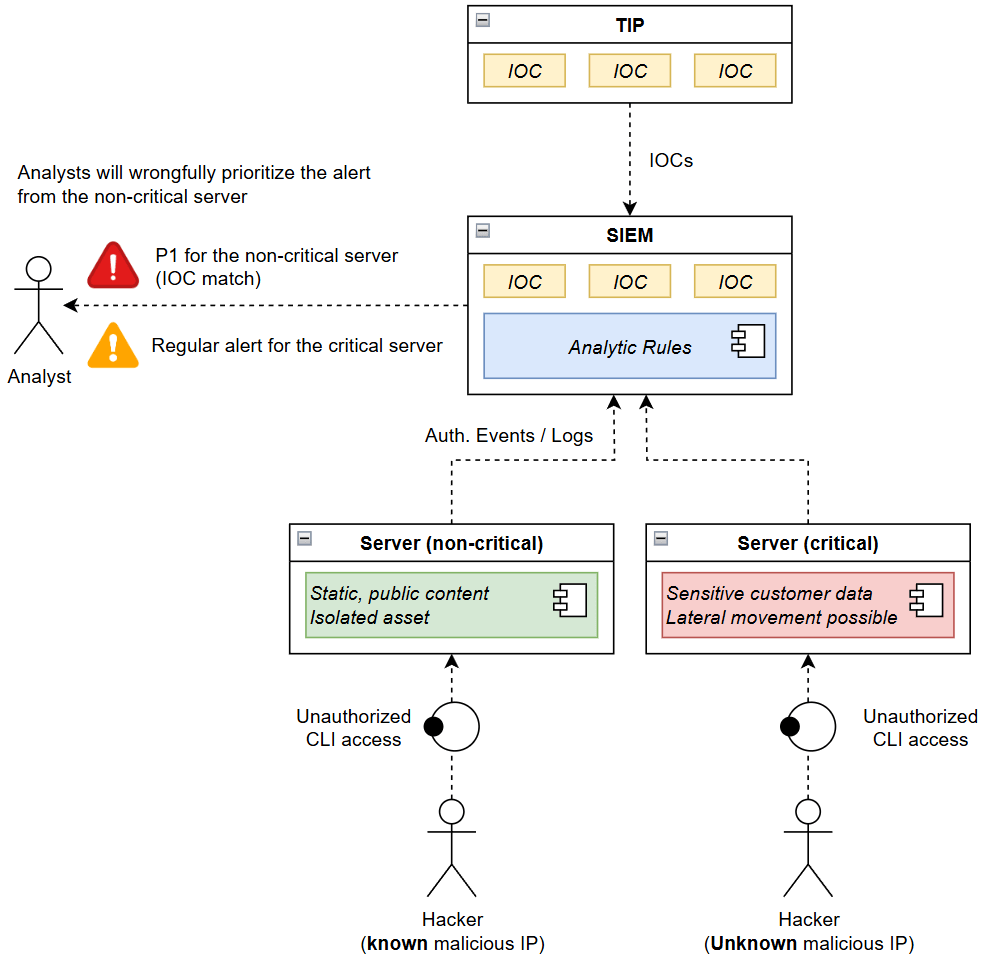
The real danger of leaning too heavily on CTI is alert fatigue. When every IOC triggers a critical alert, regardless of the target’s importance, analysts drown in noise, missing the high-impact threats that matter most.
Possible Improvement: The company could leverage its CMDB to assess the potential impact of each breach, beyond the IOC itself. The alert for the non-critical server would be deprioritized, while the critical server triggers an immediate investigation, even if the hacker’s source IP was not part of the IOCs received from the TIP.
Conclusion: To truly prioritize alerts and catch sophisticated threats, MDR teams need to pair CTI with organization-specific context (hence full contextual analysis), like asset criticality and user behavior. Only then can they see the full picture and focus on what truly keeps the business safe.
Building Full Contextual Analysis: Components and Solutions
As seen above, contextual analysis is critical for proper detection and CTI alone, while a good start, is far from enough to provide sufficient protection as it focuses on the known attacker landscape only, not your specific environment.
Here are some recommendations to get closer to a full contextual understanding of your systems:
- Asset Inventory with CMDB: Maintain up-to-date inventory of systems and data, classified by business value (e.g., via a CMDB)
- User and Entity Behavior Analytics (UEBA): Leverage UEBA to maintain baselines of user and system behavior to detect anomalies, such as unusual access patterns.
- Environmental Context: Properly document your network topology, system dependencies, and business processes to assess an alert’s ripple effect.
- Stakeholder Context: Prioritize incidents based on user roles, using platforms like Microsoft Entra ID to flag high-value stakeholders.
Let’s use a final real-life scenario to illustrate UEBA:
Issue: An employee with access to a financial database downloads a large file at 2AM in the morning. Threat intelligence shows no IOCs, as the activity originates from a trusted IP, and MDR teams do not consider the event critical as they get a lot of similar events during business hours. Without context, the alert might be labeled as informational or even dismissed.
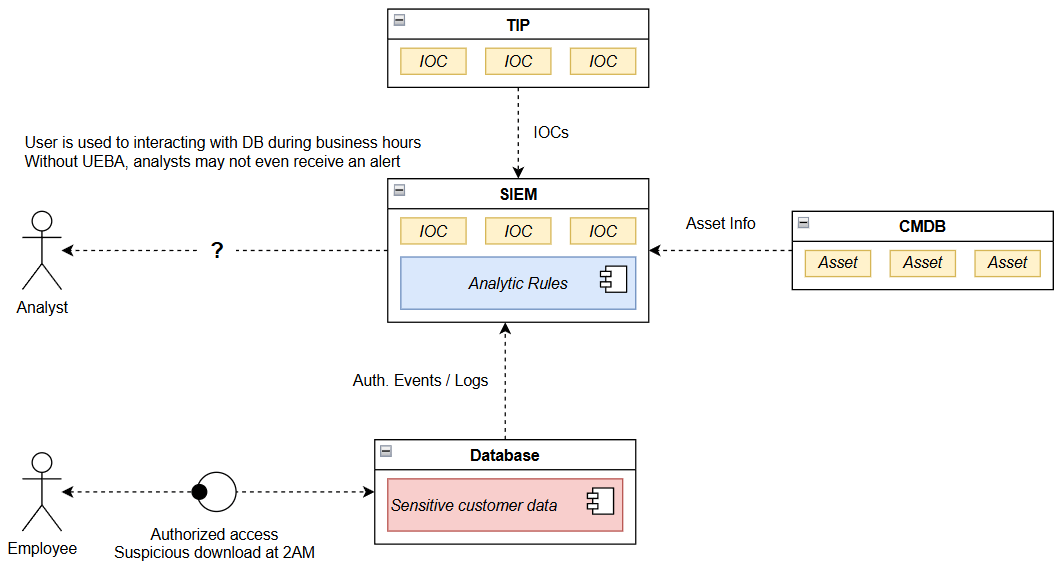
Possible Improvement: Using UEBA, the MDR team could detect that the employee’s downloads deviate from their baseline behavior (e.g., accessing files at 2 a.m., far exceeding typical volume). Contextual analysis, combining UEBA with asset criticality, flags the database as high-value, prompting an investigation that uncovers an insider threat.
Conclusion: UEBA and asset context enable detection of subtle threats missed by threat intelligence alone.
Conclusion
Full contextual analysis is transforming cybersecurity by enabling MDR teams to move beyond static rules and threat intelligence. By integrating attacker-focused data with organization-specific context, teams can prioritize alerts based on their true impact, reduce noise, and detect sophisticated threats. As cyber attacks grow more complex, adopting contextual analysis is no longer optional: the future of cybersecurity lies in our ability to see the full picture and connect the dots.
